What do leaders who are skilled at navigating complexity know how to do? What do they do differently? What would you observe if a leader had these skills?
That’s the question Tom (author of the Innovation Tactics card deck) and John posed themselves in a recent conversation. These skills are typically lumped under “soft skills” and “culture fit”.
But what if we made them explicit?
We started by describing general behaviors (“What would we observe?”) and then wrote definitions in the standard “the ability to…” format. We tried to keep the descriptions reasonably lingo-free.
We also included sample interview questions just in case you might want to try to hire people who have these capabilities or prepare for an interview at a company that might be looking for someone with these capabilities.
Note: In this post we used the word “capabilities” because while individuals shape their environment, many of these capabilities emerge as properties, behaviors, and “abilities” of groups of people—not single individuals.
Accept We Are Part of the Problem
The ability to recognize and accept one's role in creating, contributing to, or perpetuating the current situation.
Interview Question:
Can you share a specific instance when you recognized your contribution to a problem? What led to this realization, and how did it influence your actions in the future?
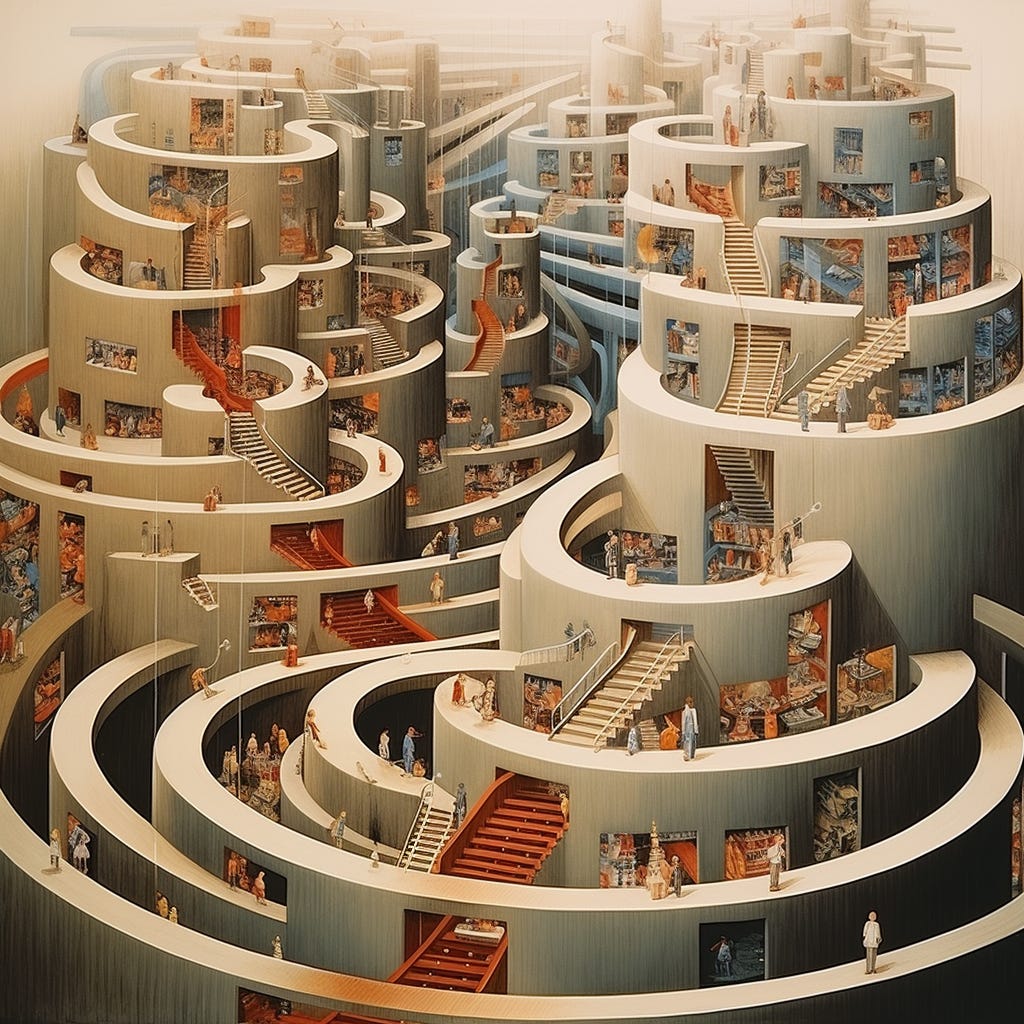
Encourage New Interaction Patterns
The ability to encourage new interaction patterns within an environment rather than solely attempting to change (or remove) individuals. Help individuals connect and become exposed to new information and experiences.
Interview Question:
Describe a situation where you facilitated new ways for people to interact or share information. Or a situation where you exposed people to new kinds of information or experiences. What prompted you to make the change, and what was the outcome?
Patient Divergence
The ability to encourage productive divergence and resist the urge to converge on a solution or path forward prematurely. Fostering an environment conducive to creative exploration and following multiple "threads", allowing alignment to happen without forcing it.
Interview Question:
Tell me about a time when you guided a team through a complex issue without rushing toward a solution. How did you manage this process, and what led to finally deciding on a path forward?
Identify Plausible Contributors / Multiple "Causes"
The ability to identify multiple factors that could plausibly contribute to a problem, and to hold them all in mind even when some may seem contradictory. This includes resisting the urge to try to isolate a single root cause explanation.
Interview Question:
Discuss a complex problem you've encountered with numerous contributing factors. How did you tackle this complexity, and what was your method for deciding what to do next?
Power of the Present
The ability to harness the potential in the present context and situation instead of defaulting to identifying an idealized future "goal state" and "gap" as the only viable path to improvement. Starting where things are now and exploring adjacent options, instead of focusing solely on what we would ideally like the situation to be. The ability to identify and learn from what is working in the present and amplify that to overcome obstacles (versus focusing solely on what is broken, who is struggling, etc.)
Interview Question:
Often as leaders we struggle with the tension between two extremes. At one extreme, we push for a big leap towards our opinionated vision about where we want to get to. At the other, we start where we are right now, figure out what’s working, and take small steps to change the present situation. Can you describe a situation where you needed to explore this tension?
Blend Diverse Perspectives
The ability to seek diverse perspectives, especially those that challenge our beliefs and defaults. Resist seeking to be the most informed. Realize that the person who is most wrong in any situation is the one who believes they have the most holistic view. Instead see the blending of perspectives as a source of multiple possibilities, enabling many paths to emerge.
Interview Question:
Can you tell me about a time you needed to make space for many diverse perspectives, including those that you found particularly challenging? How did that inform collective decisions and actions moving forward?
Patience and Self-Repair
The ability to patiently let certain situations play out and "fix" themselves over time instead of repeatedly intervening.
Interview Question:
Can you share an example of a time you chose not to intervene in a situation, allowing it to resolve on its own? What informed this decision, and how did it turn out?
Anticipate Effects
The ability to anticipate (but not necessarily predict) the possibility of emergent behaviors and downstream Nth-order effects. Accepting that unintended effects are the rule, not the exception, we need to scan the situation for signals continuously.
Interview Question:
Can you tell me about a time you needed to try to anticipate the unintended side effects of a difficult decision? What did you watch out for?
Curiosity and Light Touch
The ability to approach situations with curiosity and a "light touch”. This means resisting the impulse to judge and act, while creating space to explore the thoughts and feelings that come up.
Interview Question:
Describe a moment you caught yourself making a snap judgment and instead opted for curiosity. What prompted this change in approach?
Both/And
The ability to recognize and appreciate the interdependence of opposing forces or ideas, understanding that many situations are not about choosing between either/or but navigating the both/and of seemingly contradictory elements. Avoid simplifying complex issues into strict trade-offs.
Interview Question:
Can you tell me about a time you faced something that looked like a simple trade-off on the surface—an either/or situation—but it turned out to be a both/and situation? How did you navigate the situation?
Intervene Safely
The ability to intervene in a situation in ways that minimize the chance of unsafe and harmful side effects and maximize the chance that positive behaviors, signals, and patterns will emerge. When harmful things emerge, the ability to quickly dampen the negative effects. When good things emerge, the ability to "amplify" and sustain those things. While we can hone this skill, it does not guarantee success or that we will be consistently right.
Interview Question:
Can you tell me about a time when you and your team tried out a new way of working, interacting, or behaving? How did you decide what to try? How did you figure out whether to double down or change again?
Abduction and Intuition
The ability to balance deduction and logic with abduction and intuition. The ability to "think outside" a narrow set of logical and obvious conclusions given a limited data set. Tapping into the human ability to make intuitive leaps given a "mess" of patterns.
Interview Question:
Can you share details about when you needed to balance logic with intuition? What was the process and outcome? How did you involve others? How did data play into this, or not?
Accept Diverse Strengths and Skills
The ability to accept and value strengths and views we do not personally hold or value. Understanding that we are not omniscient when it comes to recognizing skill and influence, and may unintentionally devalue important aspects of an individual or team.
Interview Question:
Can you tell me about a time you needed to assess strengths and skills unfamiliar to you and where there was a risk of devaluing those skills because they didn't match what you value? How did you approach the assessment?
Collaboratively Sense and Shape
The ability to engage others in making sense of and shaping the environment. Resisting the impulse to simplify problems (“we just need to ...”), or the urge to control or “own” the interpretation of a situation.
Interview Question:
Can you tell me about a time when you involved other people in making sense of a problem and then worked with them to shape the environment to allow progress to happen?
Coherence vs. Alignment
The ability to seek coherence instead of alignment—setting boundaries and "no go" areas but encouraging people to explore broadly and in multiple directions simultaneously within those boundaries. Acknowledging that forced alignment is fragile, and that generally coherent actions are resilient.
Interview Question:
Can you tell me about a situation where you were tasked with getting people to take action, and you did it without forcing everyone to align on every detail? How did you determine a generally coherent direction without defining an idealized end state?
Plant Seeds—Help Them Grow
The ability to see output as something organic that is planted/seeded and grows and evolves, not as something structured that is planned, built, and completed. Hold scope lightly, and use time as an enabling constraint instead of a requirement container.
Interview Question:
Can you tell me about an example demonstrating your approach to balancing the certainty of requirements, your use of timeboxes and timelines, and the potential for new, unexpected (and valuable) things to emerge?
Tailor Ways of Working
The ability to tailor ways of working to the situation and nature of the challenge. Based on context, mix and match:
Simple and get it done
Big and ordered plans
Experiment to achieve a predefined outcome
Looser diverse experiments, observing for emergence
…with an understanding that when humans are involved, you may want to lean towards the latter options.
Interview Question:
Can you share some contrasting examples of how you tailored your and your team's way of working based on the nature of the challenge? How did you shift how you approached planning and execution?
Facing Uncertainty
The ability to balance A) gravitating towards the most uncertain parts of a situation and B) seeking the comfort/momentum of making "quick win" progress with the better-known and more familiar parts. Seeing uncertainty as a signal of opportunity and supporting an environment that is friendly to tackling complex challenges (vs. trying to make it "simple").
Interview Question:
Can you describe a time when you needed to balance quick wins with tackling a key area of uncertainty? What was your approach? How did you support your team and enable progress and learning?
Notes
Before using the questions in a real interview, we recommend discussing these capabilities internally and answering the questions. Are these capabilities valued in your company? Do people who exhibit these capabilities thrive or encounter challenges? How does the culture of your company influence how these capabilities manifest? What words do you use to describe these things?
We likely used more jargon and theory than we should have in this post. We apologize. The ability to lead with accessible language and practical application is a capability we are working on!
Describing explicit capabilities is a minor crime against complexity. These capabilities are not inherent in individuals but are intertwined with the environment and relationships. We realize that people deep in the community will take us to task. Feedback appreciated.
There are very few contexts where you want to use these approaches with everything you do. You’d burn out your team. We noted this in the “Tailor Ways of Working” capability. We indexed on complex problems and environments for this post, but you’ll always have a distribution.
Many companies have evolved ways of handling complexity without doing it explicitly, using jargon, or labeling techniques (using the word “complexity”). The capabilities listed above may be considered triggering or foreign to you or others in your company. Keep that in mind when discussing this post. Before concluding that your company “doesn’t do this,” ask yourself how you achieve these things in your way and context.

 Why is he micromanaging how you are structuring your org or what roles you are allowed to fill? He hired you to do a job, and he’s not letting you do it. He can’t even explain why he isn’t letting you do it. This does not bode well.
Why is he micromanaging how you are structuring your org or what roles you are allowed to fill? He hired you to do a job, and he’s not letting you do it. He can’t even explain why he isn’t letting you do it. This does not bode well.
 ).
). )
) I think it misconstrues the fundamental nature of sociotechnical systems. The “socio” and “technical” of sociotechnical systems are not neatly separable, they are interwoven and interdependent. There is actually precious little that is purely technical work or purely people work; there is a metric shitload of
I think it misconstrues the fundamental nature of sociotechnical systems. The “socio” and “technical” of sociotechnical systems are not neatly separable, they are interwoven and interdependent. There is actually precious little that is purely technical work or purely people work; there is a metric shitload of 

 So is a lot of other glue work! By which I mean the work is important, but does not itself move the business forward; we should do as much of it as absolutely necessary and no more. The nature of glue work is such that it too-easily expands to consume all available time and space (and then some). Constraints are good. Feeling a bit underresourced is good, and should be the norm. It is incredibly easy for management to get a bit bloated, and managers can be very loath to acknowledge this, because it’s not like they ever feel any less stressed or stretched.[*]
So is a lot of other glue work! By which I mean the work is important, but does not itself move the business forward; we should do as much of it as absolutely necessary and no more. The nature of glue work is such that it too-easily expands to consume all available time and space (and then some). Constraints are good. Feeling a bit underresourced is good, and should be the norm. It is incredibly easy for management to get a bit bloated, and managers can be very loath to acknowledge this, because it’s not like they ever feel any less stressed or stretched.[*]